
FulcrumSec, known as The Threat Thespians, is an aggressive extortion group that just went public: a new leak site, 21 claimed victims, and two more campaigns already declared. They target enterprise cloud environments, steal data, and move quickly, publishing when victims don’t cooperate and escalating personally when they push back.
Active since September 2025, FulcrumSec has claimed targets across technology, professional services, financial, and healthcare sectors in multiple countries, despite explicitly committing in their initial outreach to never target healthcare organizations. The group targets organizations where sensitive data lives in cloud storage: AI platforms, SaaS companies, and cloud-native businesses. Two additional campaigns are already announced on their leak site, with potential victims listed by revenue in the tens of billions.

How FulcrumSec Operates
FulcrumSec is an emerging group and the full picture of their capabilities is still developing. The group has been open about their methods, publishing descriptions of their access techniques across leak site campaign pages and individual victim posts. On the Index of /Shame campaign page, FulcrumSec describes their own methods directly, noting that when not exploiting unpatched vulnerabilities they focus on organizations that have left data exposed through basic misconfigurations. The profile below draws on that self-reported activity alongside a small number of reported incidents.
Intrusion and Exfiltration
•CVE-2025-55182 (React2Shell): Allows unauthenticated remote code execution against unpatched React frontend applications. Documented in at least one intrusion where the victim had not patched for more than two months after the vulnerability was publicly listed as actively exploited, and reported in use against additional targets five weeks later.
•Dormant credentials and API keys: Abused for initial access in at least one FulcrumSec campaign.
•Open directories: FulcrumSec’s Index of /Shame campaign targets organizations with staging servers and cloud storage left publicly accessible, a path requiring no exploitation.
•Exfiltration: Conducted across cloud environments including AWS, Azure, Databricks, MongoDB, and GCP using standard platform tools.
No ransomware binary or encryption behavior has been observed across known FulcrumSec operations.
•T1190: Exploit Public-Facing Application
•T1552.005: Cloud Instance Metadata API
•T1552.001: Unsecured Credentials in Files
•T1580: Cloud Infrastructure Discovery
•T1530: Data from Cloud Storage Object
•T1213: Data from Information Repositories
•T1567: Exfiltration Over Web Service
The Extortion Playbook
FulcrumSec is aggressive with extortion and wastes little time when organizations push back or go quiet. The group monitors victim communications and counters public statements directly, has named individual executives publicly, and is quick to post data when organizations don't cooperate. The tactics below are drawn from observed behavior, reported incidents, and the group’s own published claims.
•Single-buyer auction: FulcrumSec’s stated model is to sell exfiltrated data exclusively to one buyer, hand over access credentials, delete their own copies, and publicly confirm the transaction. In their first documented campaign, the most sensitive data was reportedly sold on these terms.
•Counter-messaging: FulcrumSec monitors victim public statements. When organizations have downplayed the scope or significance of a breach, the group has responded directly with plain text data releases to contradict them.
•Narrative control: FulcrumSec works to control the story around each intrusion before victims can. In their first documented campaign, they reached out to vx-underground with a pre-packaged media kit while exfiltration was still in progress, including a breach analysis report generated using the victim’s own stolen AI platform credentials.
•Calling out executives: FulcrumSec published a post directly to a breach forum personally naming a target organization's CEO and accusing the company of criminal negligence for failing to patch CVE-2025-55182 (React2Shell) months after a patch was available, refusing to share infrastructure logs with co-tenants after the breach, and leaving vulnerable hosts exposed after being warned.
What Comes Next: FulcrumSec’s Next Targets
On their leak site, FulcrumSec has published two upcoming campaigns alongside their current operations. Both are marked “Coming Soon” and include campaign descriptions, stated targeting rationale, and previews of target organizations listed by annual revenue.
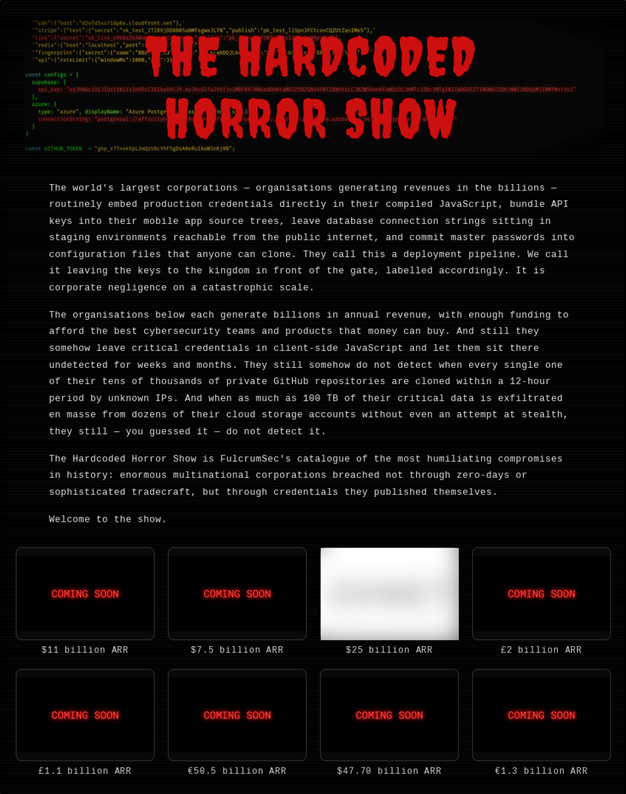
“The Hardcoded Horror Show” targets organizations that embed production credentials in client-side JavaScript, mobile app source trees, public GitHub repositories, and deployment configuration files. FulcrumSec’s campaign page claims targets failed to detect mass repository cloning and exfiltration of up to 100 TB from cloud storage. Eight teased targets are listed by annual revenue, with figures ranging up to $50 billion. Whether those claims reflect operational capability or positioning has not been verified. The focus on hardcoded credentials is directly relevant: organizations should audit compiled JavaScript, CI/CD pipelines, and Git histories for exposed keys.
“Slopocalypse Now” targets AI companies specifically, framing them as custodians of humanity’s most sensitive data whose security does not match their stated responsibilities. The campaign page cites medical conversations, financial records, legal documents, private communications, and children’s information as the data at stake.
Protecting Against FulcrumSec
Exposure to FulcrumSec runs through three consistent surfaces: unpatched public-facing applications, dormant or embedded credentials, and storage left accessible from the internet. The group has not relied on custom tooling or novel techniques, which means the window to address these gaps exists before an operation begins. The recommendations below reflect what is known about how FulcrumSec operates.
•Patch management: Prioritize patching internet-facing hosts. CVE-2025-55182 (React2Shell) is the only publicly documented vulnerability in FulcrumSec’s toolkit and should be treated as an immediate priority.
•Secret scanning: Scan Git histories, CI/CD logs, and cloud storage for exposed credentials. FulcrumSec’s Hardcoded Horror Show campaign targets organizations with this gap.
•Mandatory credential rotation: Rotate API keys, cloud service credentials, and database credentials on a defined cycle. Dormant credentials have been exploited in claimed FulcrumSec campaigns.
•Cloud account segmentation: Separate cloud accounts across distinct business entities. In one reported operation, a single compromised host reached three organizations sharing one account.
•Audit and restrict cloud storage: Eliminate publicly accessible storage buckets and staging servers. FulcrumSec’s Index of /Shame campaign targets this gap.
•MongoDB hardening: Audit MongoDB instances for public exposure. MongoDB has appeared across FulcrumSec's documented target environments.
•MFA enforcement: Implement phishing-resistant MFA across all cloud and administrative accounts. FulcrumSec requires no malware; credential access alone is sufficient for intrusion.
How MOXFIVE Can Help
Professional Services: Vulnerability assessments, control validation through EDR coverage assessments, purple team exercises, network segmentation reviews, backup immutability and restoration testing, external attack surface reduction, and SIEM/XDR detection engineering.
MOXGUARD: Strategic advisory including AD/identity assessments, CVE alerting prioritized to active ransomware exploitation, guidance on segmentation and backup hardening, tabletop exercises with response playbooks, and pre-positioned incident response.
Our team has handled hundreds of ransomware cases against the most advanced and active operations, aligning preventive, detective, and recovery controls to current threat actor TTPs. Contact us at 833-568-6695 or email our team at incident@moxfive.com.


MOXFIVE provides the clarity and peace of mind needed for attack victims during the incident response process. Our platform approach enables victims of attacks to work with a Technical Advisor who provides the expertise and guidance needed in a time of crisis, and facilitates the delivery of all technical needs required, consistently and efficiently.
Learn More
With experience on the front lines responding to incidents daily, MOXFIVE Technical Advisors have the unique ability to connect the dots between business, information technology, and security objectives to help you quickly identify the gaps and build a more resilient environment.