March 25, 2026
LiteLLM PyPI Compromise: Inside the TeamPCP Supply Chain Campaign
LiteLLM versions 1.82.7 and 1.82.8 on PyPI were found to contain a malicious payload, marking the latest development in an active supply chain campaign by TeamPCP. The campaign includes earlier March compromises of Trivy, GitHub Actions, Docker Hub, npm, and Checkmarx KICS, where stolen credentials and trusted software distribution paths were used to move from one environment to the next. Any organization that ran affected components during those exposure windows should treat the event as a credential exposure across every system those components touched.
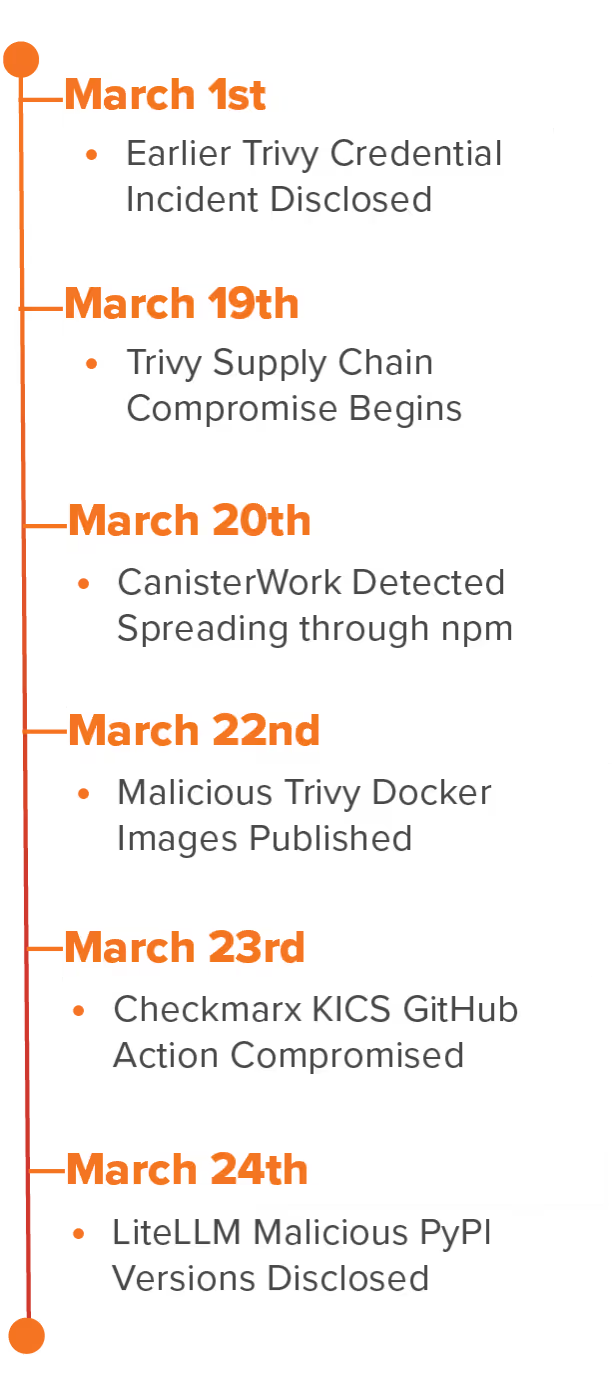
Recent TeamPCP Activity Overview
TeamPCP surfaced publicly in late 2025 targeting exposed cloud services before shifting focus to the software supply chain in March 2026. Rather than targeting applications or end-user systems, the group focused on security and development tooling that organizations grant broad access to their pipelines and infrastructure. That targeting approach, combined with a pattern of using credentials stolen at each stage to reach the next, allowed the campaign to move across Trivy, GitHub Actions, Docker Hub, npm, Checkmarx KICS, and PyPI in under two weeks.
- March 1, 2026 — Earlier Trivy Credential Incident Disclosed
An earlier incident involving credential exfiltration from Aqua Security had not been fully contained, leaving access that TeamPCP retained into the March campaign. The malicious Trivy release was not the beginning of the group's presence in that environment. - March 19, 2026 — Trivy Supply Chain Compromise Begins
Using retained credentials, threat actors published a malicious Trivy v0.69.4 release and force-pushed 75 of 76 trivy-action version tags and all 7 setup-trivy tags to malicious commits. The legitimate Trivy scan still ran after the payload, which helped affected pipelines continue to appear normal. - March 20, 2026 — CanisterWorm Detected Spreading Through npm
Stolen npm tokens from compromised CI/CD runners seeded CanisterWorm, a self-propagating worm that published malicious updates across every package owned by the stolen tokens. The worm spread across more than 64 npm packages and more than 135 malicious artifacts. - March 22, 2026 — Malicious Trivy Docker Images Published
Threat actors pushed malicious Trivy Docker images for v0.69.5 and v0.69.6 directly to Docker Hub without corresponding GitHub releases, reaching pipelines and developers pulling container images outside of the GitHub Actions exposure window.
TeamPCP March 2026
Activity Timeline
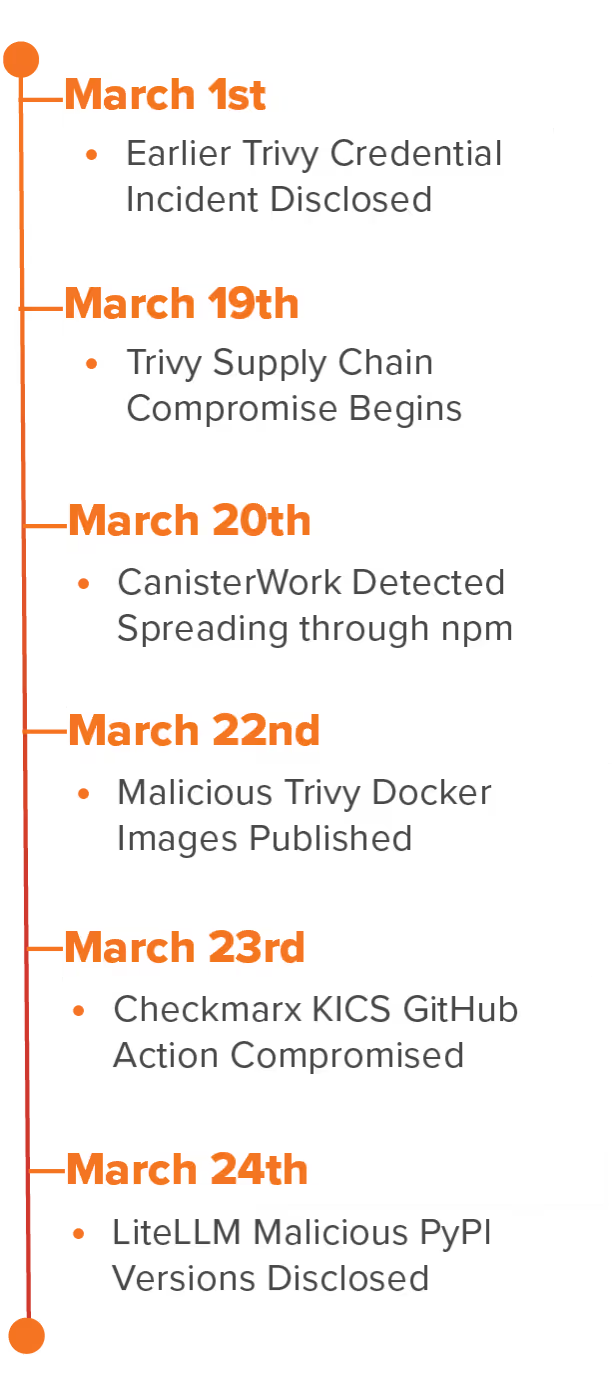
- March 23, 2026 — Checkmarx KICS GitHub Action Compromised
Using a compromised Checkmarx service account, threat actors pointed all tags in the Checkmarx/kics-github-action repository to malicious commits while the master branch remained clean. The payload carried the same RSA public key used in the Trivy compromise, providing the technical basis for linking the two operations. - March 24, 2026 — LiteLLM Malicious PyPI Versions Disclosed
Versions 1.82.7 and 1.82.8 of LiteLLM were published to PyPI with a malicious payload believed to have originated from the maintainer's CI/CD pipeline running the already compromised Trivy scanner. The compromise extended the campaign into AI development tooling and a widely used Python package.
TeamPCP did not stop after gaining access to one project. Stolen credentials and trusted distribution channels became the mechanism for moving from one environment to the next, and that pattern is what allowed a single incomplete credential rotation to cascade into a month-long campaign.
Resilience Considerations for Protecting Against TeamPCP
Determining whether compromised components were executed in your environment is the starting point, and any secrets accessible to those systems should be treated as compromised. Containing inherited access, validating what downstream workflows consumed affected components, and limiting how far a single stolen credential can travel across build and deployment environments are the priorities that follow.
- Identify and Remove Affected Components: Review CI/CD pipelines, build environments, and developer workflows for known compromised components, including Trivy v0.69.4, malicious Trivy Docker images v0.69.5 and v0.69.6, compromised Aqua Security and Checkmarx GitHub Actions, malicious LiteLLM versions 1.82.7 and 1.82.8, and known malicious npm packages. Replace impacted versions and remove mutable references that may still point to malicious content.
- Rotate Exposed Credentials and Secrets: Credentials accessible to any system that executed compromised components should be treated as exfiltrated. Rotation should cover cloud access keys, personal access tokens (PATs), SSH keys, Kubernetes secrets, package registry tokens, environment variables, and long-lived service account credentials shared across environments.
- Pin Trusted Components to Immutable References: Where GitHub Actions are used, pin to verified commit hashes rather than mutable tags. Reduce reliance on mutable release paths and introduce verification controls for third-party packages, containers, and build dependencies.
- Restrict and Monitor CI/CD Network Activity: Limit outbound access from runners to approved destinations. Unexpected external connections, archive uploads, package publication activity, and suspicious Docker API access each warrant direct investigation.
- Enforce Least Privilege Across Build Environments: Enforce least privilege across GitHub Actions, package publishing workflows, Docker environments, and Kubernetes-integrated build systems. Tokens and service accounts with cross-environment access are what allowed this campaign to move as quickly as it did.
- Scope Downstream Exposure: Determine which images, packages, releases, or workflows were consumed during the exposure windows and identify where they were executed. In this campaign, the downstream environments carried as much risk as the originally compromised projects.
Outlook for TeamPCP in 2026
TeamPCP's March campaign showed how quickly release infrastructure and service account access can become an intrusion path once credentials are not fully contained after an initial breach. Retained credentials, mutable release paths, and tooling with broad pipeline access were enough to move the operation from one environment to the next without requiring a new entry point each time. As organizations continue to rely on shared automation, third-party packages, and cloud-connected development workflows, the attack surface that enabled this campaign is not unique to TeamPCP or to March 2026.
How MOXFIVE Can Help
MOXGUARD: Strategic advisory including AD/identity assessments, CVE alerting prioritized to active ransomware exploitation, guidance on segmentation and backup hardening, tabletop exercises with response playbooks, and pre-positioned incident response.
Professional Services: Control validation through EDR coverage assessments, purple team exercises, network segmentation reviews, backup immutability and restoration testing, external attack surface reduction, and SIEM/XDR detection engineering.
MOXFIVE helps organizations prepare for and respond to software supply chain compromise across developer infrastructure, build pipelines, and cloud environments.
Contact us at 833-568-6695 or email our team at incident@moxfive.com.