Every month, we take a look at a current ransomware threat actor. If you would like to receive this via email each month, click below to subscribe to the MOXFIVE mailing list.
Additional Threat Actor Spotlights are available on our Resources page >>
NightSpire is a ransomware operation that emerged in early 2025 and has posted more than 200 victims to its data leak site across most industries, with approximately 150 of those posted in 2026 alone. Based on MOXFIVE's observations for Q1 2026, NightSpire ranked fifth among the most active ransomware operations tracked.
The group began as a closed operation and has since announced a transition to a ransomware-as-a-service model, a development that sets it apart from many operations at a similar stage. Threat actors have gained access through credential abuse and exploitation of internet-facing infrastructure, deploying native Windows utilities, credential theft tooling, and third-party software across victim environments. Once inside, the group exfiltrates data before encrypting systems and threatening to publish stolen files if the ransom is not paid.
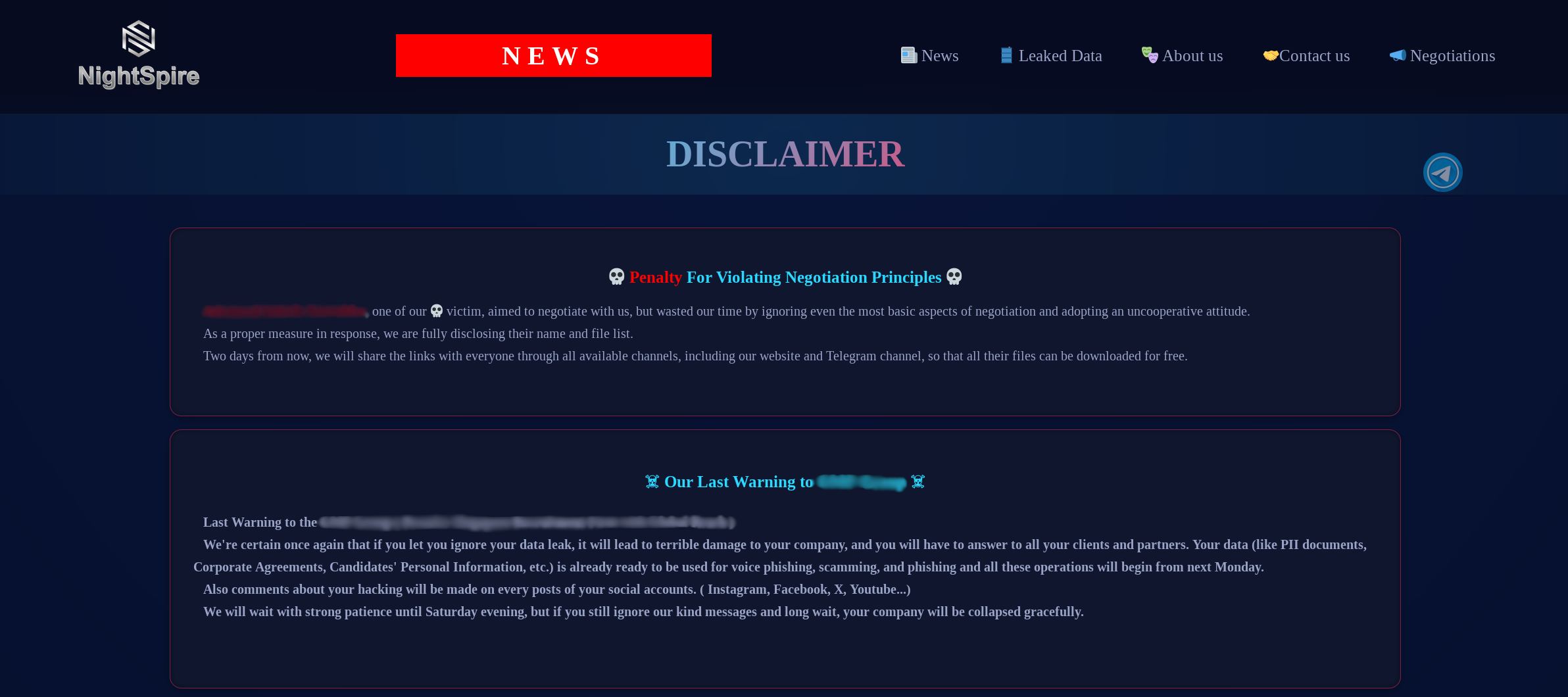
Figure 1: NightSpire data leak site.
An announcement posted to the group's data leak site indicates the operation has transitioned to a ransomware-as-a-service model in 2026. Traditionally, this means operators maintain the ransomware and supporting infrastructure while affiliates conduct intrusions and deploy the ransomware against victim organizations.
While it remains unclear whether affiliates have been brought on, the rapid increase in victims posted to the DLS in 2026 could be an early indicator of that growth.

Figure 2: NightSpire data leak site RaaS announcement.
Since the NightSpire ransomware operation first entered the wild, it has impacted organizations across most industries. Manufacturing and production account for the largest share of victims, followed by technology and healthcare. Retail and hospitality and construction and engineering round out the top five.
NightSpire does not appear to focus on a specific geography, though the United States accounts for the largest concentration of victims. France, India, Hong Kong, and Japan follow as the next most impacted countries.

NightSpire threat actors have gained access through credential abuse and exploitation of internet-facing infrastructure, with both methods observed across campaigns attributed to the group. With the group's announced transition to a RaaS model, initial access methods in NightSpire campaigns may become more diverse as affiliates bring their own tradecraft to intrusions.
NightSpire threat actors employ a double extortion model, exfiltrating data prior to encryption and threatening to publish stolen files on the group's Tor-based data leak site if the ransom is not paid. Data is staged and transferred to attacker-controlled infrastructure using file transfer and cloud storage utilities before the ransomware payload is deployed. Encrypted files are appended with the .nspire extension, and a ransom note is dropped on affected systems, with observed filenames including nightspire_readme.txt.

Campaigns where NightSpire ransomware was deployed have combined native Windows utilities, credential theft tooling, and third-party software to execute intrusions across victim environments.
MOXGUARD: Strategic advisory including AD/identity assessments, CVE alerting prioritized to active ransomware exploitation, guidance on segmentation and backup hardening, tabletop exercises with response playbooks, and pre-positioned incident response.
Professional Services: Control validation through EDR coverage assessments, purple team exercises, network segmentation reviews, backup immutability and restoration testing, external attack surface reduction, and SIEM/XDR detection engineering.
Our team has handled hundreds of ransomware cases against Qilin, Akira, The Gentlemen, and other active operations, aligning preventive, detective, and recovery controls to current threat actor TTPs. Contact us at 833-568-6695 or email our team at incident@moxfive.com.