Every month, we take a look at a current ransomware threat actor. If you would like to receive this via email each month, click below to subscribe to the MOXFIVE mailing list.
Additional Threat Actor Spotlights are available on our Resources page >>
The Gentlemen is a ransomware operation that emerged in August 2025 and has quickly become one of the more active groups to surface in the past year. The operation is believed to function under a ransomware-as-a-service (RaaS) model, with affiliates deploying the ransomware against organizations across multiple regions and industries. Since posting its first victim in September 2025, The Gentlemen has listed more than 200 victims on its data leak site. Activity slowed through the fourth quarter of 2025 before accelerating sharply into 2026, with January and February alone accounting for more than half of all posted victims.
From MOXFIVE's experience, the group employs a double-extortion model, exfiltrating data before encrypting systems and threatening to publish stolen files if ransom demands are not met. The ransomware includes variants for Windows, Linux, and ESXi environments, with threat actors observed selecting between hypervisor-level and OS-level encryption based on the environment. Intrusions show consistent use of compromised credentials and exploitation of internet-facing services for initial access, followed by methodical reconnaissance, custom defense evasion tooling, and domain-wide ransomware deployment via Group Policy. Manufacturing and production organizations have been the most frequently impacted, though targeting spans technology, financial services, transportation and logistics, and healthcare across a geographically diverse victim pool.

Figure 1: The Gentlemen data leak site.
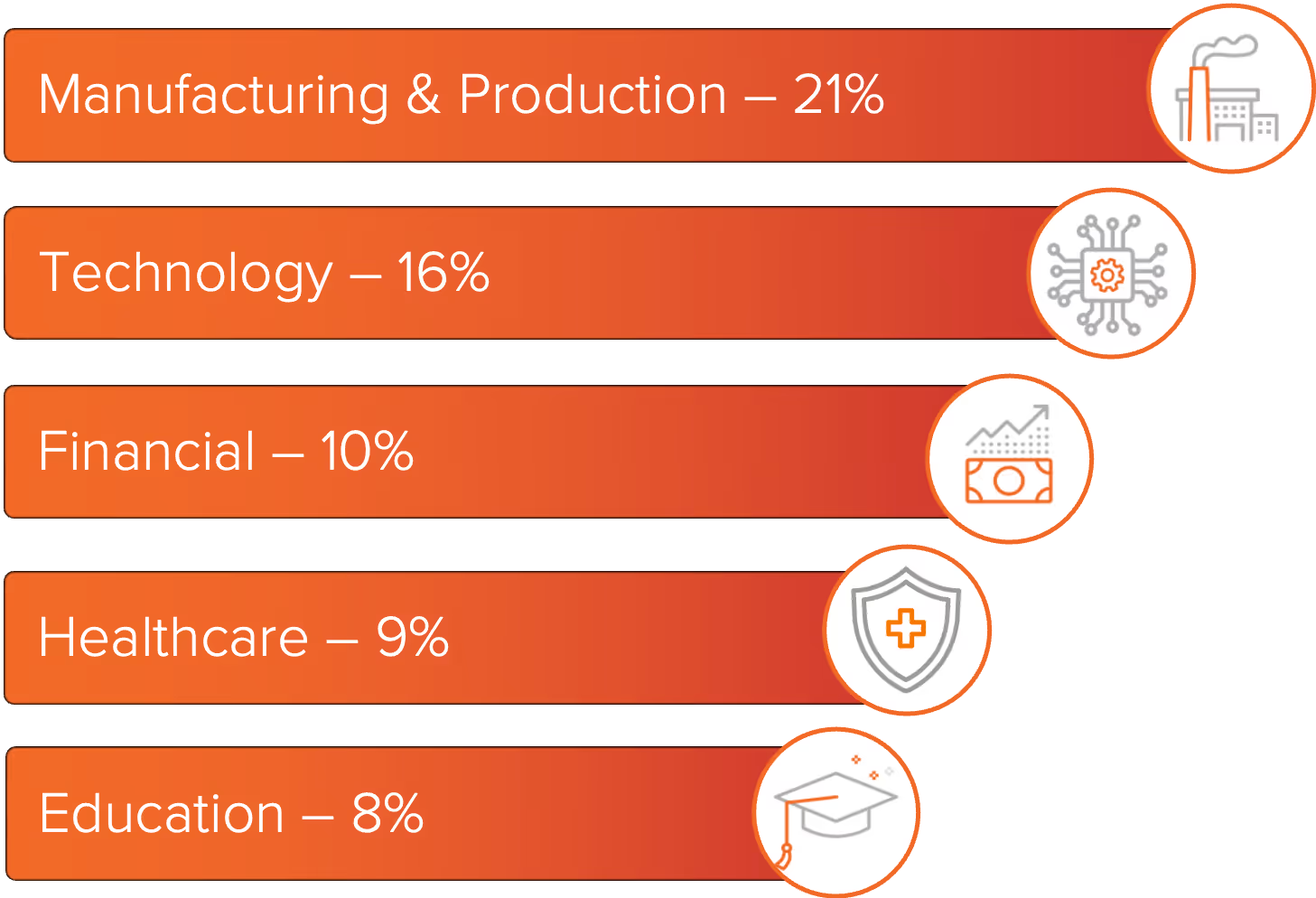
The Gentlemen ransomware has most often impacted organizations where operational disruption can quickly affect revenue and where stolen data can increase legal and regulatory exposure.
Manufacturing and production were impacted the most, followed by technology. Financial services and healthcare were next, with education also among the more frequently impacted sectors. The industry data below is based on organizations posted to The Gentlemen’s data leak site between September 2025 and March 2026.
The United States accounted for the largest share of impacted organizations, with activity observed across multiple regions. Thailand and Brazil were the next most impacted countries. Beyond those, victims were distributed across a wide range of countries in Southeast Asia, Europe, and Latin America, with no single country in those regions standing out significantly above the others.
Threat actors deploying The Gentlemen have relied on remote access pathways to establish footholds in victim environments. Incidents show a preference for credential abuse and exploitation of internet-facing services, consistent with a targeted rather than opportunistic approach to initial access.
ThrottleStop.sys (CVE-2025-7771): Disclosed in August 2025, this vulnerability allows a local attacker to read and write physical memory at the kernel level, enabling termination of protected security processes. Threat actors deploying The Gentlemen ransomware have exploited this flaw as part of a Bring Your Own Vulnerable Driver (BYOVD) chain, loading the driver to disable security tooling and clear the path for ransomware deployment.
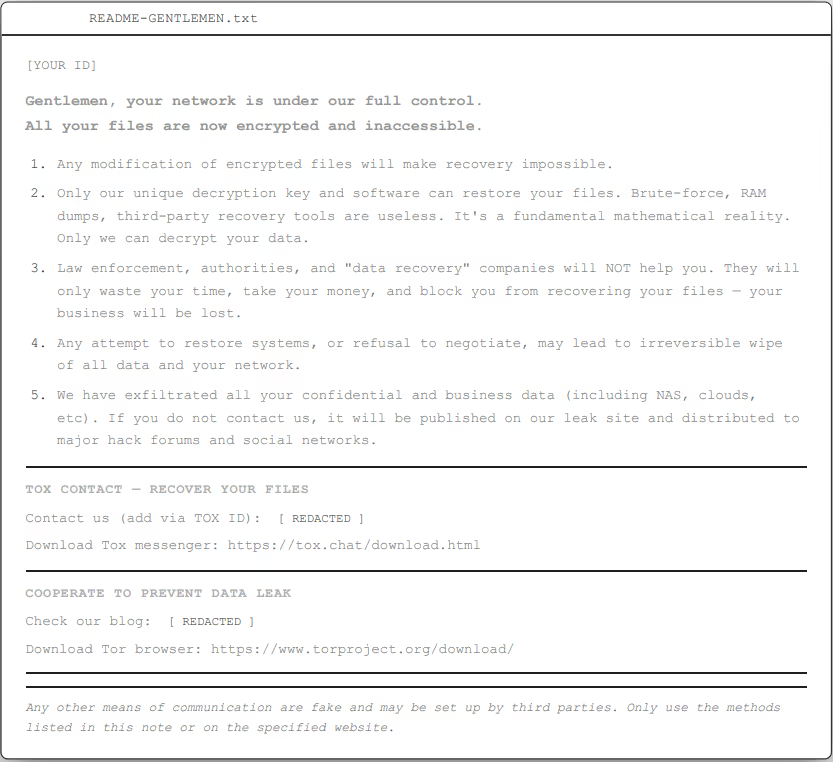
The Gentlemen uses a double-extortion model. Prior to encryption, threat actors stage and exfiltrate data before deploying the ransomware payload. Threat actors also delete shadow copies and clear Windows event logs to impede recovery and limit forensic visibility. WinSCP has been used to transfer stolen data to infrastructure under their control. Encrypted files are appended with a six-character extension, and the ransomware drops a ransom note named README-GENTLEMEN.txt on affected systems (Figure 2).
Threat actors deploying The Gentlemen rely on a combination of legitimate administrative tooling, custom evasion utilities, and Windows domain infrastructure to execute intrusions and distribute ransomware at scale.
MOXFIVE continues to track The Gentlemen activity and associated tradecraft to support organizations with detection, response, and recovery efforts.
MOXGUARD: Strategic advisory including AD/identity assessments, CVE alerting prioritized to active ransomware exploitation, guidance on segmentation and backup hardening, tabletop exercises with response playbooks, and pre-positioned incident response.
Professional Services: Control validation through EDR coverage assessments, purple team exercises, network segmentation reviews, backup immutability and restoration testing, external attack surface reduction, and SIEM/XDR detection engineering.
Our team has handled hundreds of ransomware cases against the most advanced and active operations, aligning preventive, detective, and recovery controls to current threat actor TTPs. Contact us at 833-568-6695 or email our team at incident@moxfive.com.