March was the busiest month of 2026 for ransomware activity, with victim postings across data leak sites tracked by MOXFIVE reaching their highest point of the year. Qilin led for the third consecutive month among groups posting victims in the United States, while Inc, Akira, DragonForce, and Play all posted significant victim counts across multiple industries. Interlock ransomware operators exploited a critical zero-day vulnerability in Cisco Secure Firewall Management Center weeks before public disclosure, pointing to the risk organizations face when network management infrastructure is internet-accessible. Technology and Manufacturing and Production were the most impacted industries, with Healthcare, Professional Services, and Financial organizations also targeted during the month.
Threat actors are targeting software developers as a path into production environments and software supply chains, using social engineering and poisoned package distribution to compromise developer credentials. This month's Case Study covers both vectors and the path from a single compromised developer to broader organizational compromise. The Resilience Spotlight provides guidance on hardening developer environments, covering secrets management, repository controls, and log retention.
Phishing emails, VPN vulnerabilities, lack of Multifactor Authentication (MFA), software flaws, drive-by downloads, and social engineering remain the most frequently observed initial access points for ransomware attacks.
Ransomware activity increased in March compared to previous months, with established groups driving much of the observed data leak site activity affecting organizations in the United States. Qilin, Inc, Akira, DragonForce, and Play posted the highest victim counts on their data leak sites during the month. RaaS models continued to account for a large share of deployments, with Qilin, Inc, and Akira all operating affiliate-driven programs. Outside the top five, The Gentlemen and NightSpire both saw increased activity and warrant monitoring.
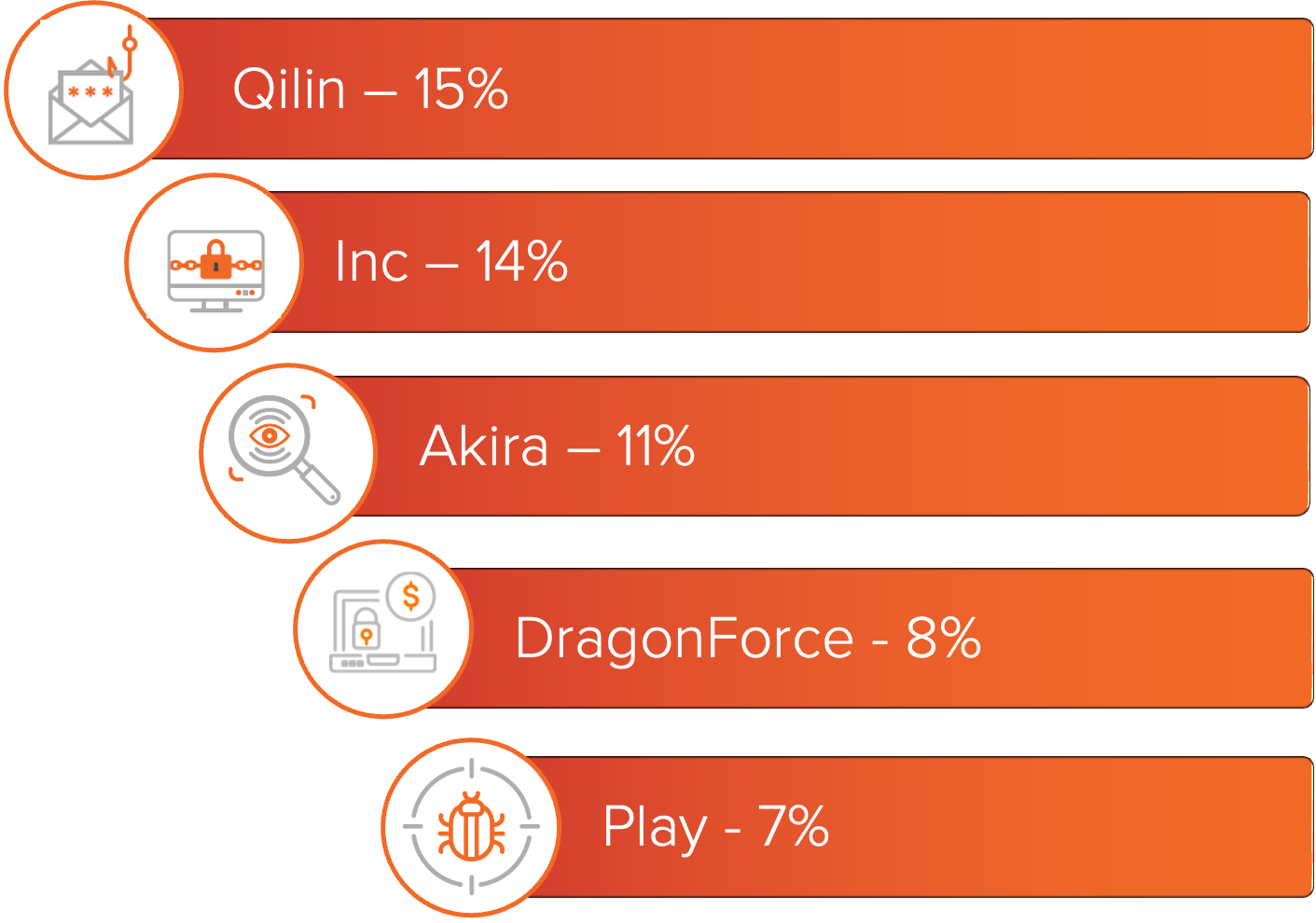
Figure 1: Top ransomware variants in March 2026 based on number of known victims.
The ransomware and industry rankings below are based on observed ransomware data leak site (DLS) activity for impacted organizations in the United States.
For a deeper look into these groups, MOXFIVE has published Threat Actor Spotlights on Qilin, Inc, Play, Akira, and DragonForce.
Technology was the most impacted industry in March. Service providers, software platforms, and managed IT firms are frequent targets due to their access to client networks and cloud environments. Manufacturing and Production ranked second, as operational disruption can quickly affect revenue, supply chains, and business continuity.
Healthcare, Professional Services, and Financial organizations also saw ransomware activity in March. Healthcare organizations continue to face risk due to the sensitivity of patient data and the impact of system downtime. Professional Services firms are consistent targets as they often hold sensitive client information and intellectual property. Financial organizations saw activity across multiple groups, where data theft and extortion can create both operational and reputational pressure.
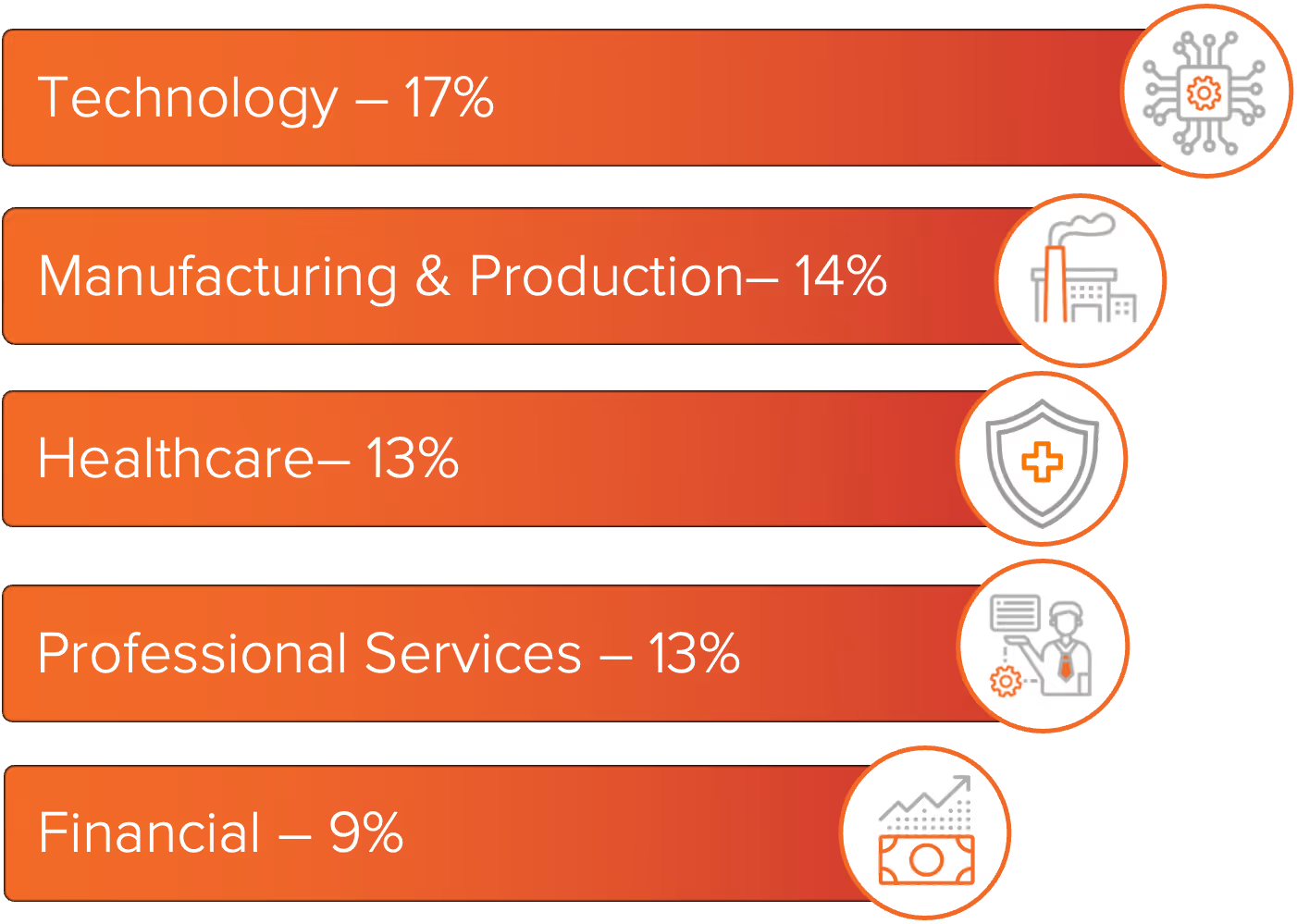
Figure 2: Top industries impacted by ransomware in March 2026.
In Technology, Coinbase Cartel and Akira drove much of the observed victim posting activity. ShinyHunters and Qilin led postings in Financial organizations. Both Coinbase Cartel and ShinyHunters are data extortion operations that rely on data theft rather than encryption, making Technology and Financial organizations notable targets for non-encryption campaigns in March. Qilin, Play, and Akira accounted for the highest victim postings in Manufacturing and Production. Genesis and Qilin posted the highest number of Healthcare victims, while Inc and Akira led activity in Professional Services.
Threat actors are targeting software developers as a path into production environments and software supply chains. These campaigns rely on two primary methods: social engineering and poisoned package distribution.
Social engineering campaigns use fake recruiting outreach, fabricated companies, impersonated identities, and branded communication channels, like Slack or Microsoft Teams, to build trust with individual developers. Once that trust is established, threat actors deliver malware through fake coding tests, malicious meeting links, or trojanized repositories hosted on GitHub, GitLab, or Bitbucket.
Poisoned package campaigns take a broader approach, modifying legitimate packages distributed through public registries such as npm and PyPI. These packages may scrape credentials from a local environment or introduce backdoors disguised as routine functionality updates. In March 2026, TeamPCP demonstrated how quickly this can escalate, using stolen credentials from one compromised tool to reach the next and spreading malicious payloads across npm, PyPI, GitHub Actions, and Docker Hub in under two weeks. A single installation by a developer, or a CI/CD run that pulls the package as a direct or transitive dependency, can provide the threat actor with execution on that developer's workstation.
In both cases, a compromised developer environment can reach beyond a single workstation to source code repositories, locally stored secrets and API keys, SSH keys, CI/CD pipeline tokens, and connected cloud environments.
Secrets exposure and weak repository controls determine how far that access reaches. Sensitive data can remain in Git history even after it is removed from the current version of a file, which is why exposed credentials should be rotated or revoked immediately rather than treated as a secondary step to history cleanup. CI/CD pipelines introduce a separate but related risk. A compromised workflow or untrusted GitHub Action can expose pipeline secrets or modify repository content, and a single poisoned Action consumed by other organizations' workflows can trigger a chain of exposure across unrelated victims. Developer-targeting intrusions also create a narrow window for incident response. Git operation events are retained for a much shorter period than broader audit log activity, which means evidence of repository cloning or code exfiltration may be gone before an investigation begins unless organizations are already streaming and preserving that data. [
A single compromised developer account can provide access across repositories, build pipelines, and connected cloud environments. The impact is greater when secrets are embedded in code, workflow permissions are too broad, or Git activity is not retained long enough to support an investigation. Organizations that lack controls at each of these layers are exposed not just to initial compromise but to cascading access that can be difficult to detect and harder to reconstruct.
How MOXFIVE Can Help
MOXGUARD: Built around a simple idea: apply the post-incident perspective before the incident. Core services cover ongoing threat and CVE alerting, monthly IR-informed briefings, AD and data risk assessments, forensic sweeps, and annual tabletop exercises. Advisory services add embedded advisors, quarterly roadmap sessions, policy and runbook alignment, and pre-positioned incident response support.
Professional Services: Control validation through EDR coverage assessments, purple team exercises, network segmentation reviews, backup immutability and restoration testing, external attack surface reduction, and SIEM/XDR detection engineering.
Our team has handled hundreds of ransomware cases against Qilin, Akira, LockBit, and other active operations, aligning preventive, detective, and recovery controls to current threat actor TTPs. Contact us at 833-568-6695 or incident@moxfive.com.